Sensors | Free Full-Text | Secure Route-Obfuscation Mechanism with Information-Theoretic Security for Internet of Things | HTML

Decomposable Obfuscation: A Framework for Building Applications of Obfuscation from Polynomial Hardness | SpringerLink

Lattice‐based obfuscation for re‐encryption functions - Cheng - 2015 - Security and Communication Networks - Wiley Online Library
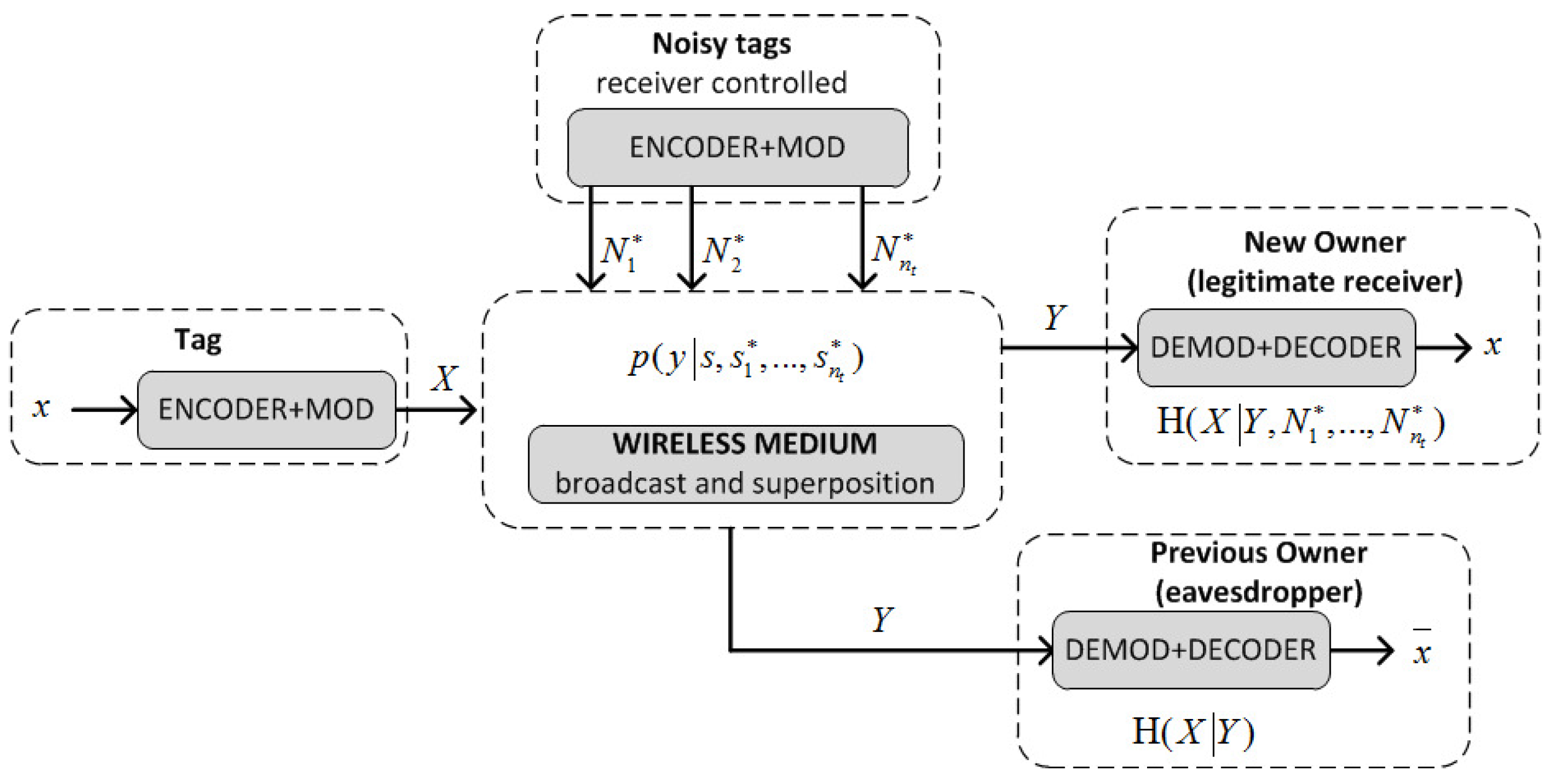
Sensors | Free Full-Text | An RFID-Based Smart Structure for the Supply Chain: Resilient Scanning Proofs and Ownership Transfer with Positive Secrecy Capacity Channels | HTML

Lattice‐based obfuscation for re‐encryption functions - Cheng - 2015 - Security and Communication Networks - Wiley Online Library
the-events-calendar/tribe-events-calendar-de_DE.po at master · nesciens/the-events-calendar · GitHub

Theoretical Foundation for Code Obfuscation Security: A Kolmogorov Complexity Approach | SpringerLink

Hardware IP Protection Using Register Transfer Level Locking and Obfuscation of Control and Data Flow | SpringerLink
PDF) Security Against Hardware Trojan Attacks Through a Novel Chaos FSM and Delay Chains Array PUF Based Design Obfuscation Scheme

Lattice‐based obfuscation for re‐encryption functions - Cheng - 2015 - Security and Communication Networks - Wiley Online Library